SPAN (Switched Port Analyzer) is a feature that allows copying traffic from a source port or switch vlan to a destination port.
In this article, we will discuss:
- SPAN Local: both the SPAN source and destination are located on the local switch. The source is one or more switch ports.
- Remote SPAN: the SPAN source and destination are on different switches. The duplicated traffic is copied through a particular VLAN across the trunk links from the source to the destination.
SPAN configuration.
Define source port or vlan:
Switch(config)# monitor session session-number source { interface type member/mod/num | vlan vlan-id}[ rx | tx | both]
Define only one destination for each session:
Switch(config)# monitor session session-number destination interface type member/mod/num [ encapsulation replicate]
The session number must be the same for the source and destination.
Example:
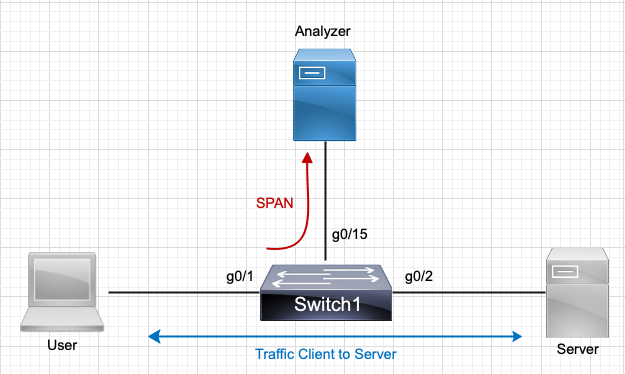
According to the above image, let’s configure a SPAN session to copy all traffic from port g0/1 to port g0/15 where the analyzer is located:
Switch(config)# monitor session 1 source interface g0/1 both
Switch(config)# monitor session 1 destination interface g0/15
Both means that incoming and outgoing traffic from the source interface will be sent (both are the default). You can use rx or tx to send traffic only in one direction.
RSPAN configuration.
Define a vlan to carry SPAN traffic between the switches:
Switch(config)# vlan vlan-id
Switch(config-vlan)# remote-span
On the switch where the source is connected, identify the source and destination RSPAN port with the following commands:
Switch(config)# monitor session session-number source {interface type member/mod/num | vlan vlan-id} [rx|tx|both]
Switch(config)# monitor session session-number destination remote vlan rspan-vlan-id
On the destination switch, you must re-identify the RSPAN source and destination using the following global configuration commands:
Switch(config)# monitor session session-number source remote vlan rspan-vlan-id
Switch(config)# monitor session session-number destination interface type member/mod/num [ encapsulation replicate]
Here the roles are reversed. RSPAN packets are extracted from the RSPAN VLAN and placed on the destination, either a physical switching interface or a Layer 2 VLAN.
Example:
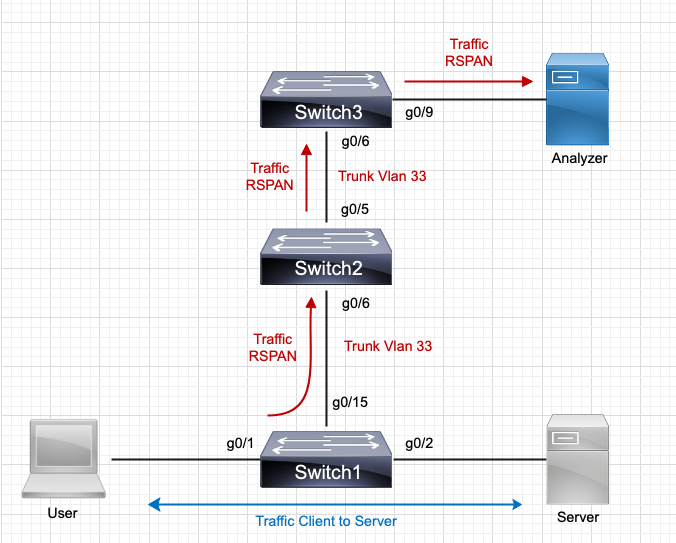
According to the diagram, the RSPAN source is port g0/1 of switch1, and the objective is to get it to the analyzer, which is on port g0/9 of switch 3 via vlan 33.
!Switch1 configuration
!Create RSPAN vlan, define RSPAN sessions and propagate vlan 33 on trunk port g0/15.
Switch1(config)# vlan 33
Switch1(config-vlan)# remote-span
Switch1(config)# monitor session 1 source interface g0/1 both
Switch1(config)# monitor session 1 destination remote remote vlan 33
!Switch2 configuration
!Create vlan 33 and allow it on the trunk links to Switch 1 and 2
Switch2(config)# vlan 33
Switch2(config-vlan)# remote-span
!Switch3 configuration
!Create vlan 33, allow it on the trunk links to Switch 2 and configure the RSPAN session to port g0/9
Switch3(config-vlan)# vlan 33
Switch3(config)# remote-span
Switch3(config)# monitor session 1 source remote vlan 33
Switch3(config)# monitor session 1 interface g0/9
Verification Commands:
Switch# show monitor
Switch# show run | i monitor